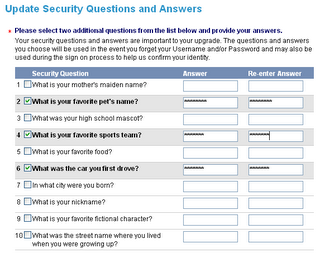
I went to sign on to the citibank site today, and before I could complete the sign-on, I was presented with the following required step:
This whole approach is just so darned awful.
This data isn't secret. Some is public record, like where I was born. Other things, like my favorite pet's name, are not pieces of data one normally protects. It's much easier to amass a collection of unprotected facts, and use those to pose as someone, than to compromise an actual password, an encryption scheme, etc. Moreover, most of these questions are used by many sites for the same purpose. So if I know someone's nickname, street address growing up, city of birth, mother's maiden name -- all readily available in the U.S. -- I'm that person on a lot of websites.
Personally, I use Mr. Schneier's approach of typing in random gibberish, thereby protecting myself at the cost of some convenience if I do lose my password.
While I'm on the topic -- and I'm sure someone has written authoritatively on it before, but nevertheless ... -- I am surprised how rarely people realize that their unprotected email account is the weakest link for all of their "secure" online activity.
Many sites (including Skip) email a new password to a user upon request. The gmail account that they stay logged in to, or log in to from a questionable computer in a hotel lobby, thinking, "My life is so boring, hey if someone wants to read my gmail, let them" ... or a business email account accessed on the road in the clear ... these become the easy way to get passwords.
There's nothing inherently wrong about using email to do a password reset (reset -- that means only a temporary password is sent via email; the user must then change it to a more protected one). Folks just need to realize that the email account -- if it is registered with sites that send passwords -- needs to be protected. Complex password, routine changes, all that...
Subscribe to:
Post Comments (Atom)

6 comments:
I bet you didn't heard about this writing service before https://homework-writer.com/blog/usa-high-schools. It would help every schooler with a homework!
Do you need a help with your paper? Try this service https://nerdymates.com/blog/writing-mistakes. They would help to every student!
Do you think they are harmful? That's weird. Check https://college-homework-help.org/blog/research-paper this page later, friend.
I agree with you. Sometimes this security questions push me off from visit many sites. This is annoying part of our life and we can't escape from this. I decided to write Problem Solution Essay about web sites and them security for my studying work in the University. Your article very helped me.
I agree, I am amazed at how quickly our world is changing. And the introduction of any technology into our lives is something amazing. As a freelancer, I write a lot on similar topics (as an example)
https://unitconversion.io/blog/how-to-write-case-brief-tips/ so I can safely say that your post is useful and important for people like me who are trying to find more useful information.
oighjgjjjt5
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
golden goose outlet
Post a Comment